Research
Our current research spans a wide spectrum of topics, including:
-
Software Security
- General
-
Program Analysis
-
Binary Analysis
- General
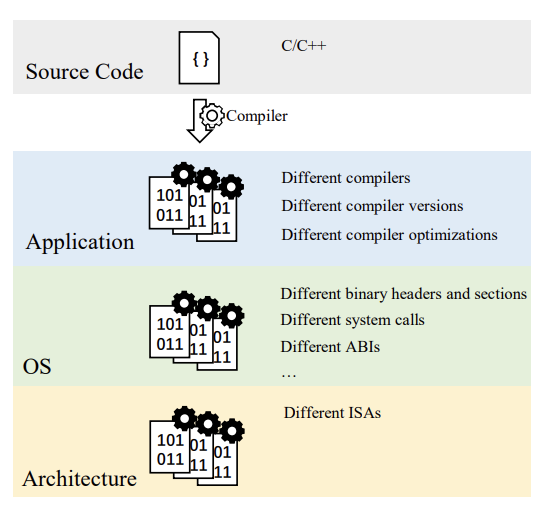
- Heterogeneous Binary
-
Binary Analysis
-
Program Testing
-
Fuzz Testing
- General
- Directed Fuzzing
-
Fuzz Testing
-
Hardware Security
-
Trusted Execution Environments
- Remote Attestation
- Hardware-Software Co-Design
-
Trusted Execution Environments
-
Machine Learning Security
- General
- Adversarial Examples
- Machine Learning Systems
-
Cryptanalysis
- Differential Cryptanalysis
Publications
2026
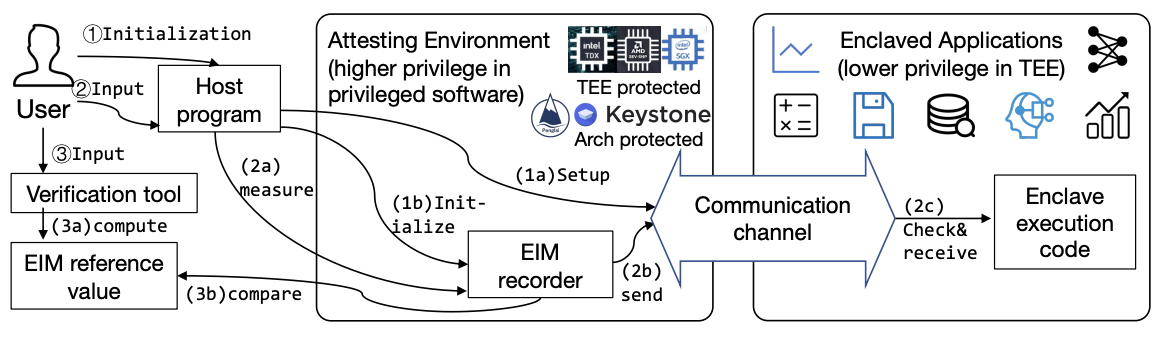
EXIA: Trusted Transitions for Enclaves via External-Input Attestation
NDSS Symposium 2026
·
01 Feb 2026
·
[no id info]
2025
An Enhanced and Robust Data Publishing Scheme for Private and Useful 1:M Microdata
IEEE Transactions on Big Data
·
01 Aug 2025
·
doi:10.1109/tbdata.2024.3495497
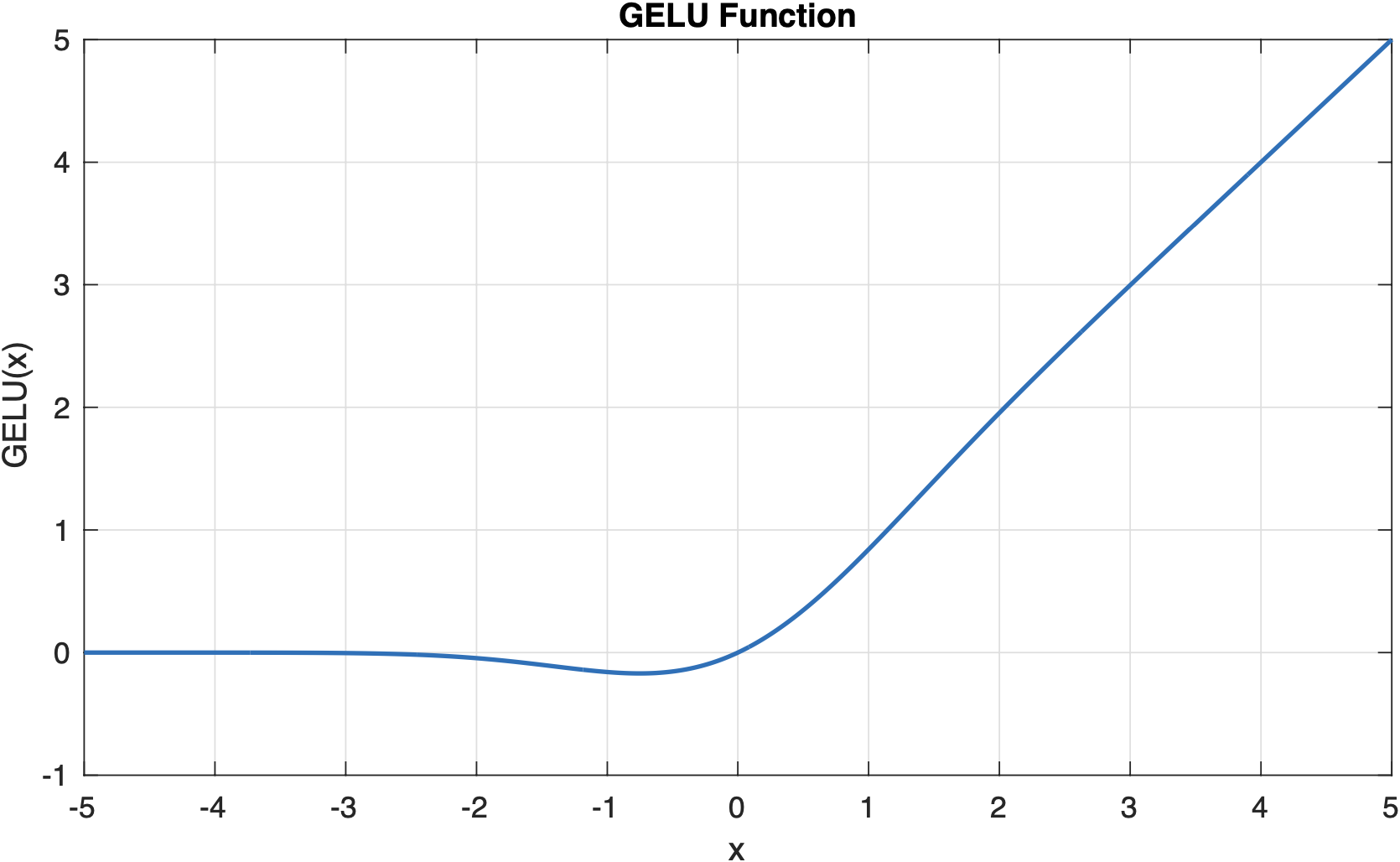
Extractions of NLP models with Derivative Analysis
DARPA Resilient Software Systems Colloquium
·
01 Jun 2025
·
[no id info]
2023
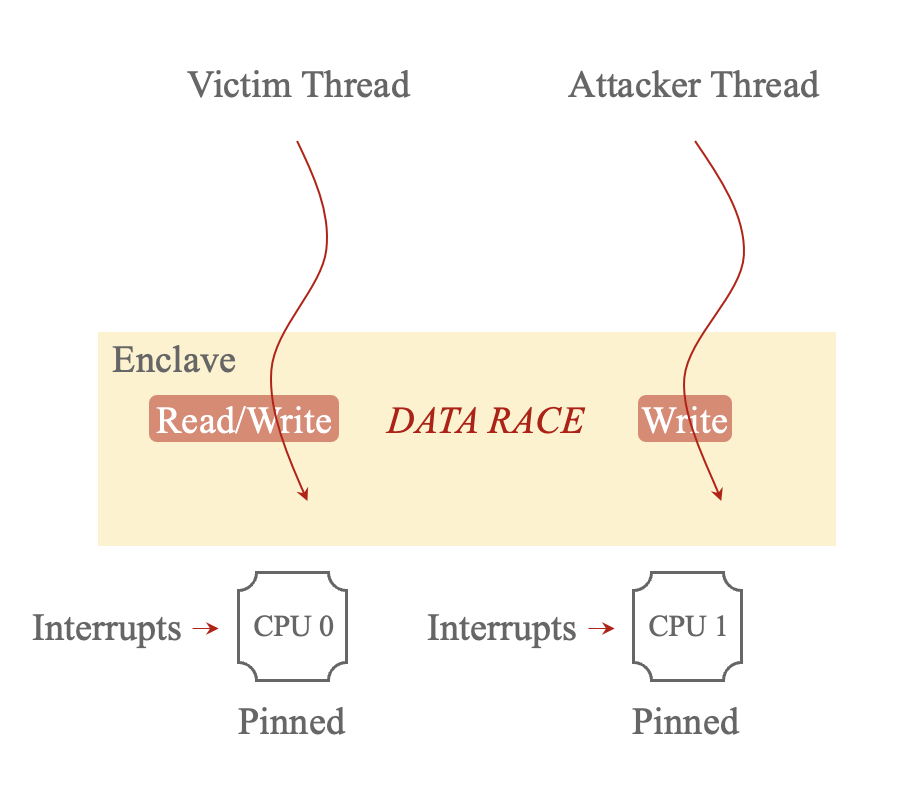
Controlled Data Races in Enclaves: Attacks and Detection
USENIX Security Symposium 2023
·
01 Jan 2023
·
[no id info]
2021
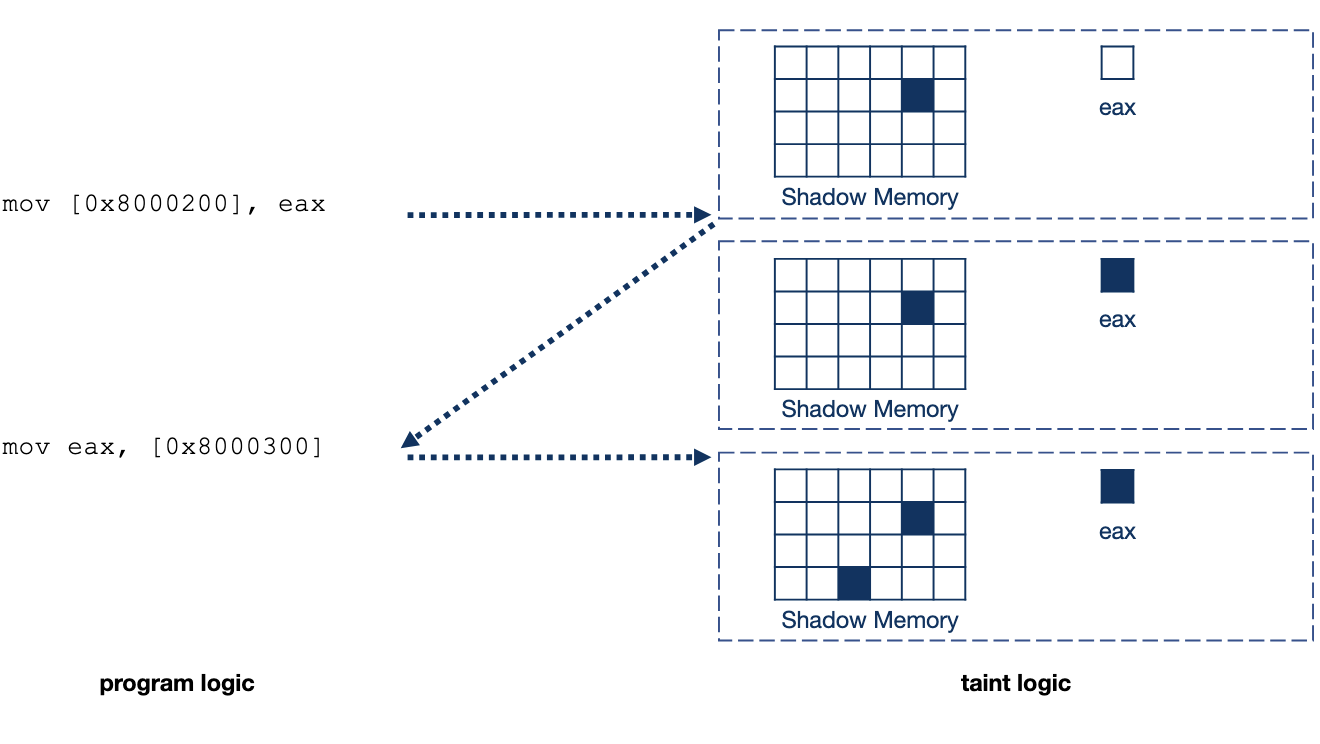
SelectiveTaint: Efficient Data Flow Tracking With Static Binary Rewriting
USENIX Security Symposium 2021
·
01 Jan 2021
·
[no id info]
Exploring Value Set Analysis for Binary Code Hardening and Vulnerability Detection
Ph.D. Dissertation
·
01 Jan 2021
·
[no id info]
2019
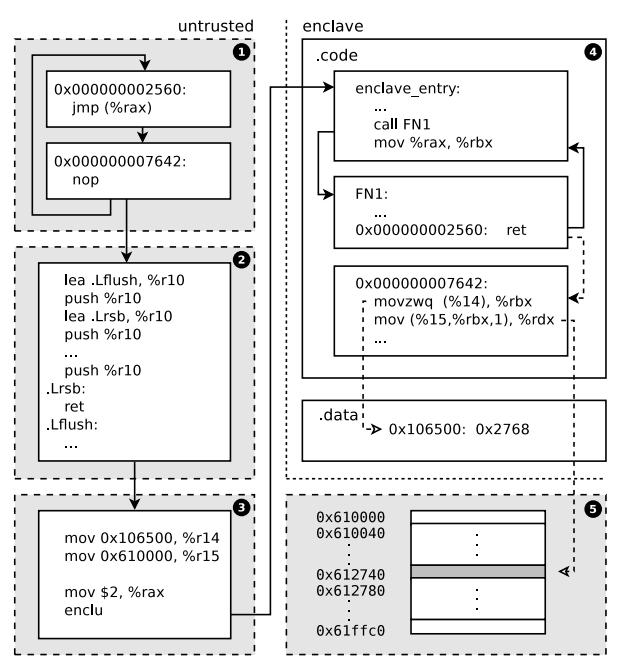
SgxPectre: Stealing Intel Secrets from SGX Enclaves Via Speculative Execution
2019 IEEE European Symposium on Security and Privacy (EuroS&P)
·
01 Jun 2019
·
doi:10.1109/eurosp.2019.00020
2018
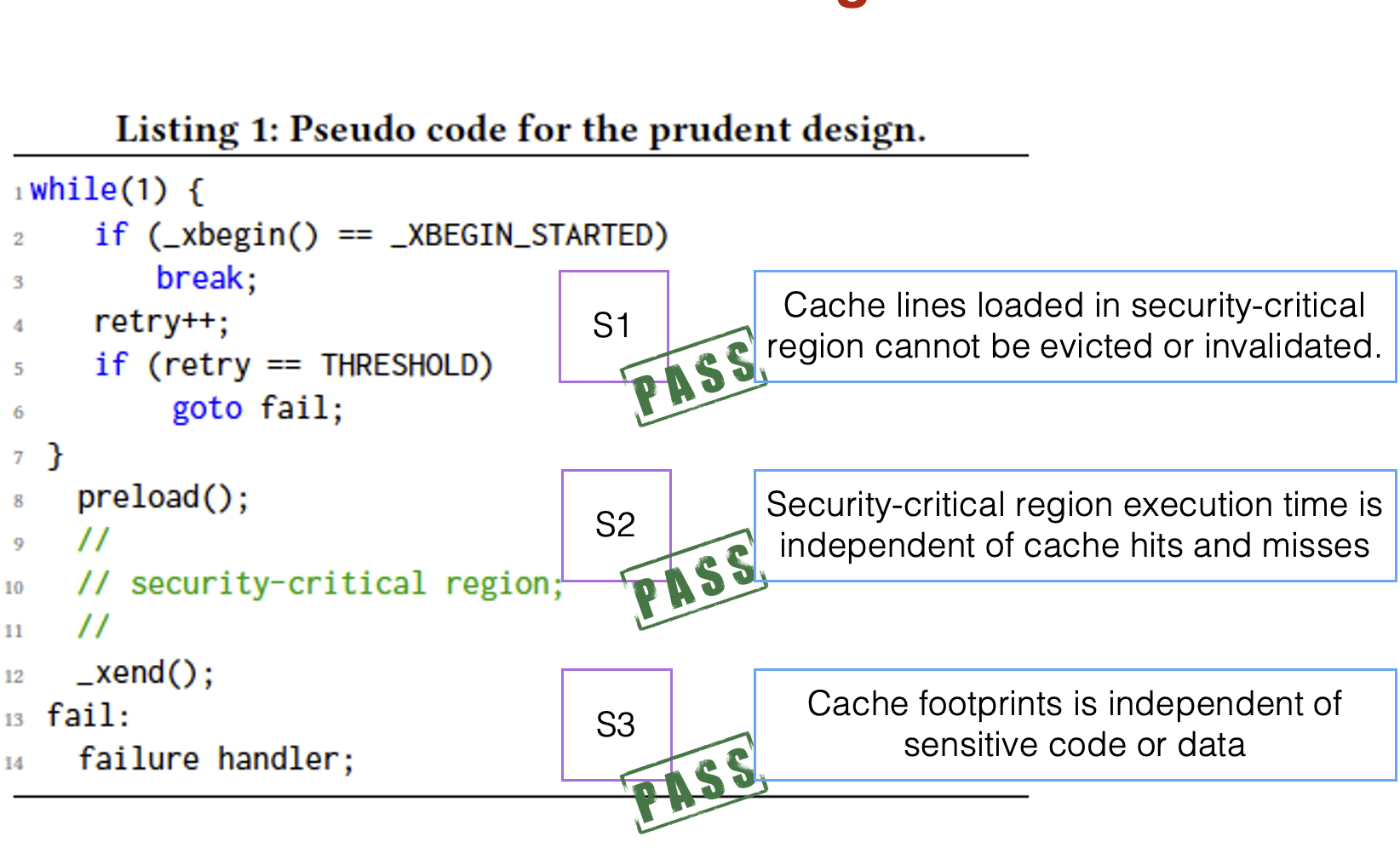
Leveraging Hardware Transactional Memory for Cache Side-Channel Defenses
Proceedings of the 2018 on Asia Conference on Computer and Communications Security
·
29 May 2018
·
doi:10.1145/3196494.3196501
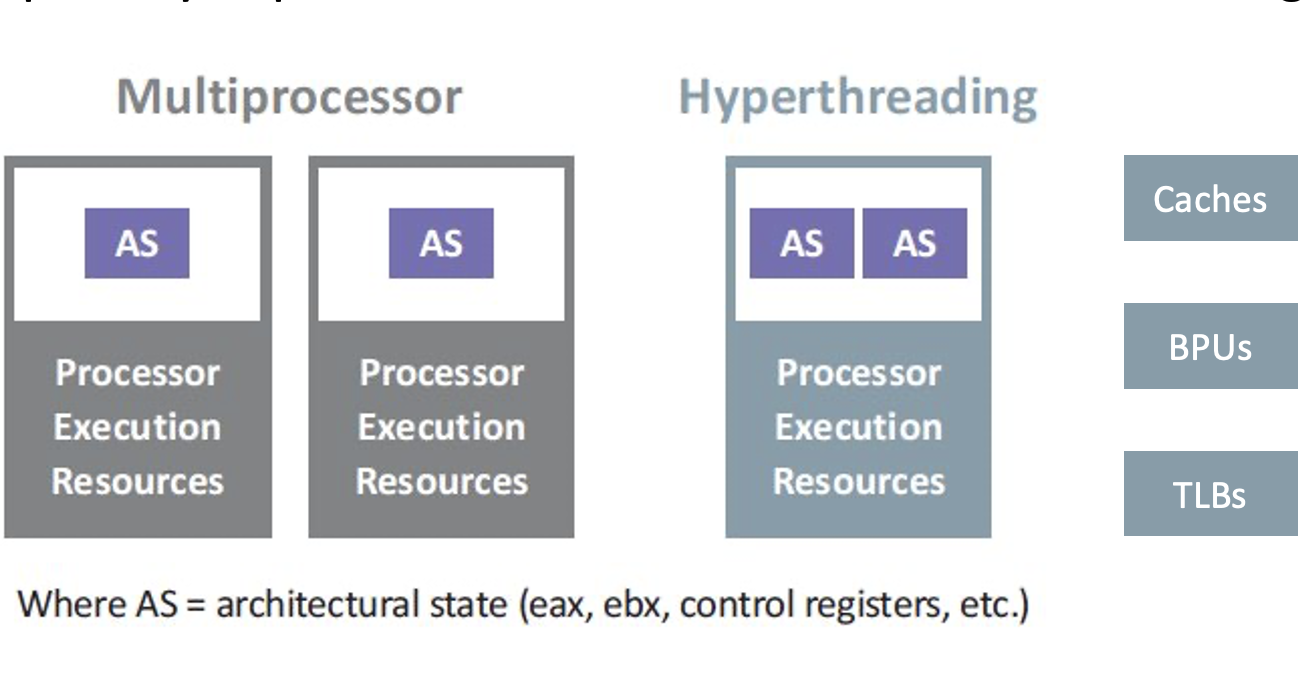
Racing in Hyperspace: Closing Hyper-Threading Side Channels on SGX with Contrived Data Races
2018 IEEE Symposium on Security and Privacy (SP)
·
01 May 2018
·
doi:10.1109/sp.2018.00024
2017
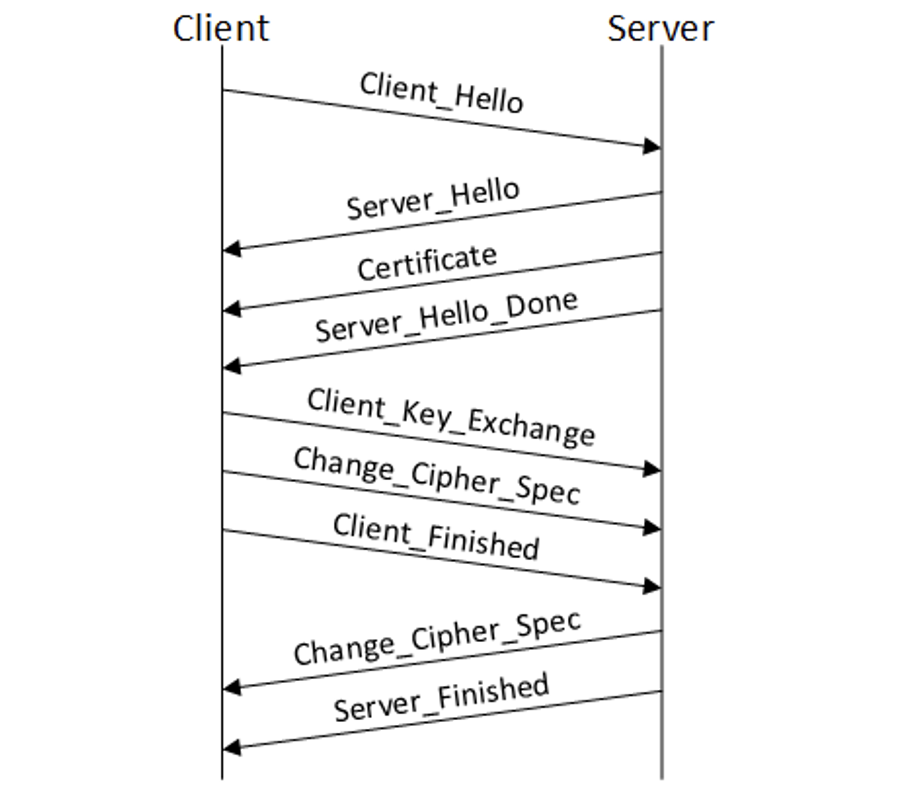
Stacco: Differentially Analyzing Side-Channel Traces for Detecting SSL/TLS Vulnerabilities in Secure Enclaves
Proceedings of the 2017 ACM SIGSAC Conference on Computer and Communications Security
·
30 Oct 2017
·
doi:10.1145/3133956.3134016
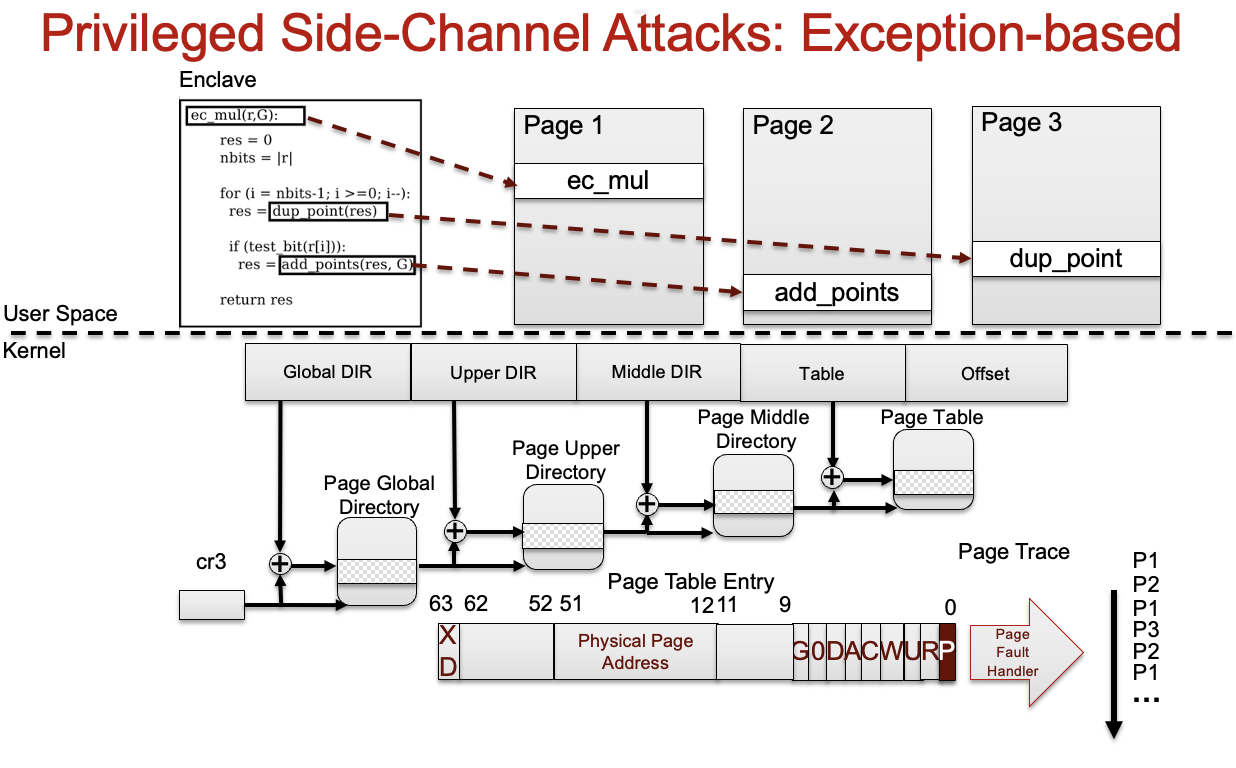
Detecting Privileged Side-Channel Attacks in Shielded Execution with Déjà Vu
Proceedings of the 2017 ACM on Asia Conference on Computer and Communications Security
·
02 Apr 2017
·
doi:10.1145/3052973.3053007
